5.10 Ethernet Networks
5.10 Ethernet Networks
Ethernet is by far and away the most popular physical medium for local area networks. Although there have been several kinds of cables, cable topologies, connectors, and speeds in Ethernet history, the basic hardware, protocol specification, and programming techniques have proved remarkably robust. Figure 5-3 on the next page shows the physical appearance of an Ethernet network.
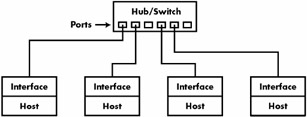
Figure 5-3: A twisted-pair Ethernet local area network.
Ethernet networks have always been cheap, but the unshielded twisted-pair (UTP) devices that gained popularity in the 1990s are now inexpensive almost to the point of absurdity. Many new computers (and devices such as video game consoles) have built-in Ethernet interfaces. Old twisted-pair networks operate at 10 megabits per second and are called 10Base-T networks. The current standard is 100Base-T (running at 100 Mb/s); it's sometimes called Fast Ethernet. 100Base-T requires category 5 cable, and 10Base-T devices work with most 100Base-T switches and hubs. If you need something a little bit faster, you can go to Gigabit Ethernet; 1000Base-T uses twisted-pair like its predecessors, and 1000Base-SX is the fiber-optic version. If you don't run a supercomputer center, it's unlikely that you'll need anything like this — you'll be hard-pressed to saturate a 100Base-T network.
To build a network, you need a network interface card (NIC) for each of your computers, a hub or switch, and some cables to connect the computers to the hub or switch. If you run out of network ports, it's easy to add another hub or switch.
Each node on an Ethernet network has a hardware address, also called the MAC (Media Access Control) address. Running ifconfig -a shows yours; in the example in Section 5.4, the hardware address was 00:40:05:A0:7F:96.
The first three bytes of a MAC address make up a vendor code, or OUI (Organizationally Unique Identifier). For example, Sun Microsystems' OUI is 08-00-20. You can look up an OUI at http://standards.ieee.org/regauth/oui/index.shtml. You do not need to bother with the MAC address except when debugging.
| Note? |
Each node on your network should have a different MAC address even if two Ethernet cards are of the same model, and most Ethernet devices carry a label with the MAC address. Unfortunately, you may come across a batch of NIC cards with a duplicate address or two. You could try to return the duplicates, but many modern cards also allow you to change the MAC address with an extra utility. |
5.10.1 Ethernet and IP
IP over Ethernet is very straightforward. When you want to send a packet to some other host on your local area network, your machine must know that host's MAC address. Using a series of ARP (Address Resolution Protocol) broadcasts, your host maps the IP address of the target to the target's MAC address and then sends the IP packet out on the wire to that MAC address.
Your host also caches the destination MAC address inside the kernel. To view your system's current ARP cache, run the following command:
arp -a
If you don't have DNS working yet, use arp -na instead, to disable hostname resolution. Linux arp with no arguments gives a slightly more formatted list than either of the above options, but this format is not standard across all versions of Unix.
| Note? |
Remember that ARP only applies to machines on local subnets. To reach destinations outside your subnet, your host sends the packet to the router, and it's someone else's problem after that. |
The only real problem you can have with ARP is that your system's cache can get out of date if you're moving an IP address from one network interface card to another, because the cards have different MAC addresses (for example, this can happen when testing a machine). Unix systems invalidate the ARP cache entry if there is no response after a while, so there shouldn't be any trouble other than a small delay for invalidated data. However, if you want to delete an ARP cache entry immediately, use this command:
arp -d host
You can also view the ARP cache for a single network interface like this:
arp -i interface
The arp(8) manual page explains how to manually set ARP cache entries, but you should not need to do this.
| Note? |
Don't confuse ARP with RARP (Reverse Address Resolution Protocol). RARP transforms a MAC address back to a hostname or IP address. Before DHCP became popular, some diskless workstations and other devices used RARP to get their configuration, but RARP is rare today. |
5.10.2 Private Networks
Let's say that you decide to build your own network at home or at the office. You have your Ethernet cards, hub or switch, and cables ready. Your next question is, "What IP subnet should I use?"
You can pay your ISP for a block of Internet addresses if you need real Internet routing to a number of individual hosts inside your local network. However, this costs a lot of money and isn't useful for anything but a highly decentralized site, such as a university. As a much less expensive alternative, you can pick a subnet from the addresses in the RFC 1918 Internet standards document, shown in Table 5-2 on the next page.
|
Network |
Subnet Mask |
Short Form |
|---|---|---|
|
10.0.0.0 |
255.0.0.0 |
10.0.0.0/8 |
|
192.168.0.0 |
255.255.0.0 |
192.168.0.0/16 |
|
172.16.0.0 |
255.240.0.0 |
172.16.0.0/12 |
Unless you plan to have more than 254 hosts on a single network, pick a small subnet such as 10.0.0.0/255.255.255.0, which uses the addresses 10.0.0.1 through 10.0.0.254. (Networks with this netmask are sometimes called class C subnets. This term is technically somewhat obsolete but still useful in practice.) You can carve up private subnets in any way that you please, experimenting to your heart's content.
So what's the catch, you say? It's very simple — hosts on the real Internet know nothing about these private subnets and will not route to them. With no extra help, your hosts cannot talk to the outside world. Therefore, if you have a single Internet connection, you need to have some way to fill in the gap between that connection and the rest of the hosts on your private network. Network Address Translation (NAT) does exactly this; see Section 5.14. Refer back to Figure 5-1 on page 94 for an illustration of a typical network. The gateway can be a regular Linux machine or one of the devices described in Section 5.9.1.






