Securing Your Mac
An important preventive maintenance task is to protect your Mac from other people who use it or from those who access its files from a network. You can also use keychains to help you manage your own security information.
Securing Your Mac with User Accounts
You should create user accounts for everyone who uses your Mac. In addition to the features that user accounts provide, such as a Web site and well-organized file storage, user accounts prevent unauthorized users from changing the system configuration of your machine.

Securing Your Mac with Privileges
For those who access your Mac over a network, you can control the access to specific items by setting privileges for those items. You can control access in several levels of privilege from not being able to even see the item to being able to read and write to it.

Securing Your Mac with Keychains
For security and other reasons (such as making online shopping more convenient), you need usernames and passwords to access network resources, whether those resources are on a local network or on the Internet. After using even a few of these, you will have a large collection of usernames and passwords. Remembering these can be a challenge. Fortunately, your Mac lets you store all your usernames and passwords in a keychain. You can then apply your keychain to whatever resource you want to use and the appropriate information is provided so that you can access what you need. All you need to remember is the password, called a passphrase, which unlocks your keychain.
You can configure your keychain so that you can gain automatic access to secured resources during each working session. To secure those resources again, you can lock your keychain, which means that the passphrase must be entered for that keychain to be applied.
Before you can use a keychain, one has to be created. A keychain is created automatically for each user account you create. However, you can create additional keychains for specific accounts if you need to.
To use a keychain, it must be unlocked. To unlock a keychain, you enter its password when you are prompted to do so. When you log in to your user account, the default keychain for that account is unlocked automatically.
Adding a Keychain
Sometimes, you might want to add a keychain to your current account. For example, if you create a new user account, you might want to move your current keychain to the new account. You can add a keychain to your user account using the following steps:
-
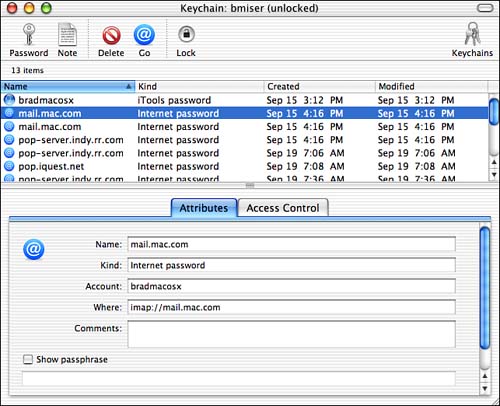
Open the Keychain Access application (Applications/Utilities directory). You will see a keychain that is called by the short name for your user account (see Figure 27.5). In the keychain's window, you will see a list of all the usernames and passwords that are stored in it, and the date that each was created or modified.
Figure 27.5. This keychain can access the items listed in the window; several are for various e-mail accounts.
-
To add a keychain, choose File, Add Keychain.
-
Locate the keychain you want to add, select it, and click Open. The keychain will be added to your user account and you will be able to access the resources contained in it.
You can see all the keychains installed for your user account by choosing View, Show Keychains. A drawer will appear and each keychain installed in your user account will be listed. Locked keychains are marked with the closed lock icon. Open keychains have the open lock icon.
Adding Items to a Keychain
After you have created a keychain, you can add items to it in the following ways:
When you access a network resource, such as a file server, look for the "Add to Keychain" check box. When you check this, the username and password for that resource will be added to your keychain.
Drag a network server onto the Keychain Access window.
Drag the Internet Resource Locator file for a Web page onto the Keychain Access window.
Manually create an item.
TIP
You can create an Internet Resource Locator file by dragging the icon next to the URL for that resource from the Internet application to your Mac. For example, in Internet Explorer, the icon appears immediately to the left of the address in the address bar. When you drag this icon onto your Mac, an Internet Resource Locator file is created. Open this file to move to the source at which it points.
NOTE
If a Web site uses a cookie to store information about your account (usually sites that don't include sensitive information in your account) and you enable your browser to accept cookies, you don't need to add it to your keychain.
One of the best uses of a keychain is to store user accounts and passwords for Web sites you access. The simplest way to add such an item to your key is to use drag and drop.
CAUTION
For the drag-and-drop method to work, your username and password must be encoded in the URL for which you create an Internet Resource Locator. If it isn't, when you access that item, you won't be logged in to your account.
-
Open the Web page you want to add to your keychain.
-
Drag its Internet Resource Locator icon from the Web browser to your keychain. This icon is located near the URL in the Address bar. You will be prompted to enter the username and password for the site.
-
Enter the username and password for the site, and click Add.
CAUTION
Not all applications support keychain access. If a particular application or resource doesn't support keychains, you won't be able to access that resource automatically. However, you can still use Keychain Access to store such an item's username and password for you, thus enabling you to recall that information easily, and it is stored more securely than writing it down on a piece of paper.
To manually add an item to your keychain, perform the following steps:
-
Open Keychain Access.
-
Open the keychain to which you want to add the item (your default key is opened automatically) by choosing Keychains and then the keychain you want to change.
-
Choose File, New, New Password Item to see the New Password Item dialog box.
-
Enter the name of the item in the Name box. If you are adding an Internet resource, such as a Web page, enter its URL.
-
Enter the username for the item in the Account box.
-
Enter the password for the item in the Passphrase box.
-
Click Add. You will return to the keychain's window and see the new item you added, and you will be able to access that item using your keychain.
TIP
You can set the default keychain for your user account by opening the keychain you want to make the default one and choosing File, Make "keychain name" Default.
Using a Keychain
When you have a keychain configured for an account and it is unlocked, you can access the items that it contains without entering your username or password. For example, when you open a server, it will open for you immediately.
NOTE
By the way, this is how Mac OS X can access your .Mac account without you having to log in each time. When you create a .Mac account, it is added to the Keychain for the Mac OS X user account related to it. Mac OS X can use this Keychain to access the .Mac account without requiring that you log in manually.
To prevent a keychain from being accessed, lock it. Do so by opening the keychain and choosing File, Lock keychain name.
To unlock a keychain again, click its Unlock button and enter the password for that keychain.
NOTE
If the keychain isn't open, select it from the Keychains menu, enter the password, and click OK to unlock it.
Your keychains are stored in the Library/Keychains folder in your Home directory. You can add a keychain from one account to another account by moving the keychain file to a location that can be accessed by the second account. (For example, you can copy your keychains into the Public folder of your Home directory to enable other users to add that keychain to their own accounts.) To add a keychain to a user account, open Keychain Access under that account and use the Add button. This is useful if you want to be able to use the same keychain from several accounts. To remove an item from your keychain, select it and click Remove.
Getting Information About Keychain Items
If you are using keychain items to store information, you can get information about a keychain item. Or, you might want to get information about a keychain item to see the details about what it accesses.
TIP
Earlier, I mentioned that you should find a secure way to store password and serial number information for software. You can use Keychains to do this even if you don't actually use the Keychain to access the item. For example, you can create a Keychain item for a piece of software that you use to store that software's serial number. To do this, click the Password button to create a new Keychain item, enter the name of the application, and then enter the serial number as the passphrase. Whenever you need this information, select the item and then check the "View passphrase" check box. After you unlock the item, the serial number will appear in the passphrase field. This is a secure way to store this type of information. Of course, if something happens to your Keychains, the data will be lost too so make sure that you have it backed up.
-
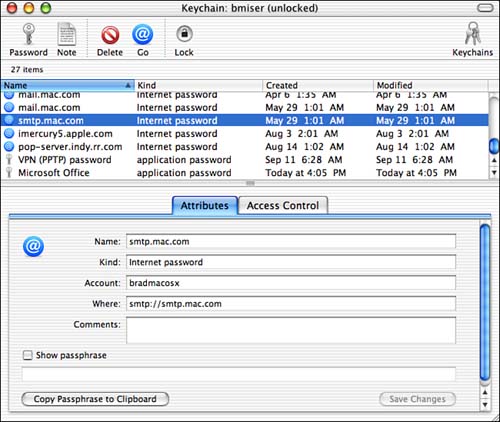
Select the keychain item about which you want information. Its information will appear in the Attributes tab (see Figure 27.6).
Figure 27.6. You can use the Attributes tab to see information about an item installed in your keychain.
-
Check the "Show passphrase" check box.
-
Confirm the passphrase by entering it at the prompt and choosing to allow access to the item. When you return to the Attributes tab, you will see the item's password.
-
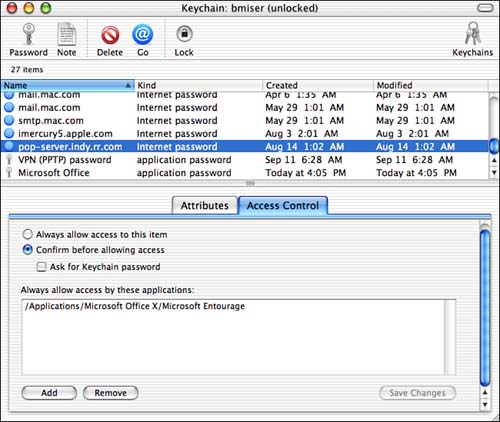
Click the Access Control tab. You will see a list of each application that has access to the keychain item.
-
Use the access controls in the window to control which applications can access this item (see Figure 27.7). In Figure 27.7, you can see that Microsoft Entourage has access to the selected keychain item.
Figure 27.7. You can determine which applications can access a keychain item by using the Access Control tab.
-
To allow access to the item without warning, check the "Always allow access to this item" radio button.
-
To allow access, but require confirmation, click the "Confirm before allowing access" radio button, and check the "Ask for Keychain password" check box if you want to be prompted for your keychain's passphrase before access is allowed.
-
To enable an application to access the keychain item, click the Add button and select the application to which you want to provide access. Then use the preceding two steps to configure the access that the application has to that item.
-
To remove an application's access to the item, select the application and click Remove.
The Keychain Access application has various other useful features, such as the following:
The Note function is used to store information in the keychain that you want to protect. For example, you can use secured notes to store serial number and registration information for applications. Your keychain's passphrase will be required to access the information stored in the note.
You can access a keychain item for an Internet or network location, by selecting the keychain item and clicking the Go button in the Keychain Access toolbar.
When prompted to enter the passphrase for a keychain, such as when an application needs to access a keychain item, you can click the Always Allow button to avoid this prompt in the future. When the application needs to access the keychain, it will be able to do so automatically.
In the keychain access prompt, you can click the Show Details link to expose the details of the keychain access being requested.
The Keychains button in the toolbar provides you with a list of all the keychains installed for your user account.







