Using a Virtual Private Network (VPN)
You've logged onto a public hotspot at some great location. This time, let's say you're connected poolside at some great hotel in a warm location. So far, all is well and good.
When you connected to the Wi-Fi hotspot provider, say T-Mobile Hotspot or Wayport, you were probably authenticated. That means you had to provide a login identification and a password, in part so that the Wi-Fi provider would know who to bill for your time online.
But beyond this authentication, there is no security at a public Wi-Fi hotspot. Transmissions are not, for the most part, encrypted. Wireless networks are inherently less secure than wireline networks because anyone can pick up the signals. Without encryption, tapping into your Wi-Fi packets as they are transmitted is like reading plain text. It is not very hard to do from a technical viewpoint.
I don't want you to get the impression that the world is full of people who live to lurk and to pick up your Wi-Fi transmissions. But you should regard a public Wi-Fi hotspot as fundamentally insecure. If you need to work with information on your home (or, more likely, office) network, this can be problematic.
caution
As specific examples of security risks that may concern you, this means that someone with the know-how and right equipment could easily sniff passwords that you provide to Web servers, read your unencrypted email, note which Web sites you visit, and track your online banking and credit card transactions. |
One solution that can be used to at least make a more secure connection from a public hotspot to your home network is to set up a Virtual Private Network (VPN) by installing a remote access server on your home network. VPNs use a dedicated server to "tunnel" through the Internet and provide a way to communicate securely with your home network as shown in Figure 18.4.
Figure 18.4. A VPN tunnel creates a secure communications channel across the insecure Internet.

This means that using a VPN is a very helpful way to add security to a Wi-Fi connection. After you've logged into the VPN, you can use the resources of your home network without feeling that security is compromised.
There are a great many vendors of VPN server products, which are mostly geared at the enterprise. For a good source of information about VPNs, and to find the companies that are involved in making the server software, you might want to have a look at the Web site for the Virtual Private Network Consortium, better known as VPNC, www.vpnc.org. The VPNC is the trade association for companies that make VPNs.
It's good news that the client software for use with a VPN is baked into the Windows XP operating system.
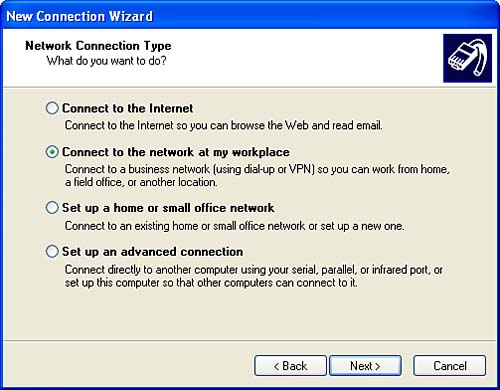
To make a connection to a VPN from Windows XP, open the Network Connections applet by double-clicking Network Connections in Control Panel. In Network Connections, click Create a New Connection (you can find this on the left under Network Tasks). When the New Connection Wizard opens, click Next.
Choose Connect to the Network at My Workplace, as shown in Figure 18.5, and click Next.
Figure 18.5. Choose Connect to the Network at My Workplace to start the wizard that creates the VPN client on your remote system.
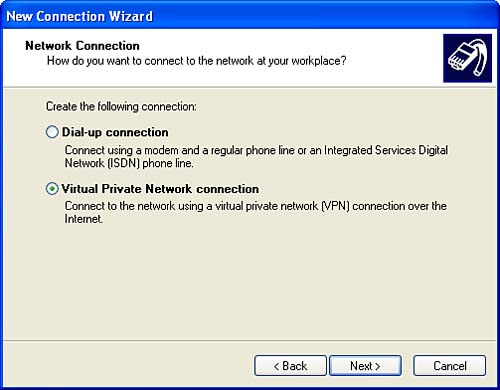
Choose Virtual Private Network Connection as shown in Figure 18.6, and click Next.
Figure 18.6. To create a VPN, choose Virtual Private Network Connection.
As you probably realize, there are some costs (in time and trouble if nothing else) in maintaining a VPN server. This is probably not something that is worth doing unless you have a number of remote users who need secure access to your home network on a regular basis. |
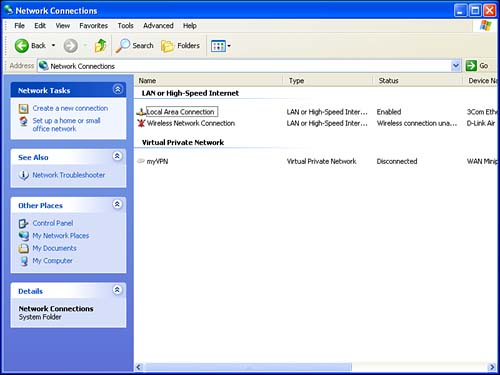
You will be asked to provide a name for the VPN, such as myVPN, and the host name or IP address of the VPN server.
Click Finish to close the wizard. The VPN will now appear in your Network Connections window, as you can see in Figure 18.7.
Figure 18.7. The new VPN is shown in the Network Connections window.
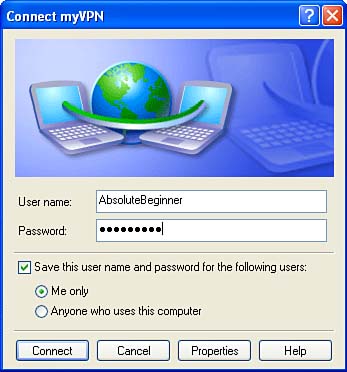
When you attempt to connect to the VPN, you will be prompted for your VPN user name and password so that the VPN remote access server can authenticate you, as shown in Figure 18.8.
Figure 18.8. When you connect to the VPN, you will be asked to supply a logon and password so that the VPN's remote access server can authenticate you.