What Steps Should You Take?
The steps you should take depend on how important the security of your personal network is to you. Some people will feel it more important than others to implement comprehensive security measures. But some of the basic security measures you can take are easy, and involve little (or no) trouble to set up and little extra trouble on the part of network users. So everyone should take at least some security measures.
The measures described in this section cover network security. Besides the measures explained in this chapter, you should also take steps to protect individual computers such as installing antivirus software and personal firewall software, as I explained in Chapter 18. |
This section will help you understand the security measures you can take, and how to implement them. It will also help you develop a security game plan in the context of your own requirements for security.
The security measures described in this chapter fall into three categories, or levels. I'll note each measure with which category it falls into, and explain any wrinkles related to the level.
The levels for security measures that I use are
No-brainer: I don't give a rat's bottom about security, and I've got nothing of any value on my network anyway, but this measure is easy to implement, and no trouble to use, so why not?
Middling: I'm reasonably concerned about security, but I don't want to waste too much time on it. I'm willing to go to a little bit of trouble to make my network more secure.
Red alert: I am really concerned about security (perhaps I deal with confidential materials belonging to clients). I can't take any chances that my network is insecure, and I'm willing to go to the additional trouble and expense that this might imply.
The National Institute of Standards and Technology, which is a branch of the United States Department of Commerce, has prepared a comprehensive white paper about wireless network security. The white paper contains a very helpful and comprehensive wireless LAN security checklist containing 45 items. The items are characterized as "best practice" (meaning it should be done) and "may consider" (meaning for those who are a little more concerned about security). A draft of this white paper is currently available at http://csrc.nist.gov/publications/drafts/draft-sp800-48.pdf. |
In order to come up with a game plan for implementing security on your Wi-Fi network, you should sit back for a moment and see which of these security levels makes the most sense to you.
No-Brainer Security
The measures described in this section are the ones that everyone with a Wi-Fi network should take (that means you!):
Change the SSID, or network name, from its default (see Chapter 14 for details).
Set the SSID not to broadcast (see Chapter 14 for details). If your SSID is not broadcast, it will be harder for a nefarious evildoer to log on (or even know your Wi-Fi network is there).
Implement WEP (wired equivalent privacy) encryption as explained in Chapter 15, "Configuring Your Wi-Fi Network."
Make sure all the computers on your network are running antivirus software, and that the virus definitions are updated weekly (see Chapter 18 for more information). This has more to do with general network protection (and common sense) than it does with Wi-Fi network security, but it is still very important.
caution

WEP encryption should not be regarded as the final solution to security problems. With the right tools, WEP encryption can be cracked in less than 15 minutes.
Change the default password for the administrative application for your access point. For example, to change the password for the Linksys Wireless Broadband Router, open its administrative application as explained in Chapter 14. Click the Password link to open the Password panel. Enter, and re-enter, the new password as shown in Figure 19.1. Click Apply to make the new password permanent.
Figure 19.1. You can use the administrative application for your access point to change its password, making it harder for intruders to take control of the access point.
[View full size image]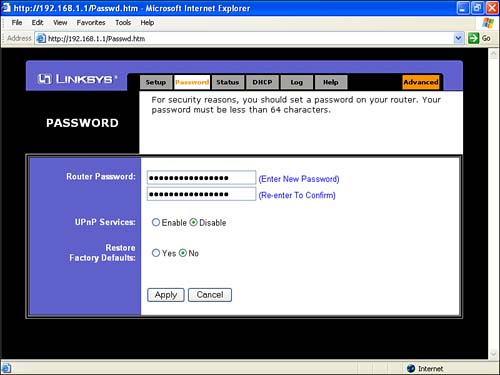
PICK YOUR PASSWORDS WISELYFor security reasons, you should be careful about the passwords you pick. Never use as a password the name of your company, anyone in your family, or your pet hamster (these are all easy to guess). For the same reason, don't use your date of birth or street address. The worst kind of password is one based on personal information that can be easily determined (or guessed). But you should also avoid passwords based on numerical sequences (such as 12345) or words (such as "password"). Better passwords are at least eight characters long, and include both letters and numbers: for example, "d31TY9jq". caution
Unless no one ever visits your home or office, don't jot down your important network passwords on a post-it, and then stick the post-it on your computer monitor. |
Middling Security
You should consider using some of the middling security measures described in this section if you have some security concerns, and are prepared to take some trouble over security, but still don't want to go overboard.
These measures include the following:
Plan to change your WEP encryption key regularly, perhaps once every week.
Engage MAC filtering, as explained later in this chapter.
Use the DHCP settings in your router (or access point/router combination) to limit the number of IPs that can be used in your network to the actual number of devices that you simultaneously connected to the network.
Red-Alert Security
Red-alert security measures are intended for use with networks that truly have confidential and proprietary information to protect and are willing to go to considerable trouble and expense. You should realize that protection at this level is not a one-shot affair: You have to constantly be on the lookout for new vulnerabilities. You'll need to keep surveying your wireless site, keep changing your passwords, and generally just keep on your toes. Expect red-alert security measures to take time and money, be trouble to maintain properly, and possibly to slow your network down!
caution
No wireless network can ever be completely secure. Keep any truly confidential information off a wireless network. |
If you really need a high level of security, you should consider not using a wireless network at all, or at the very least bringing in a qualified wireless network security expert.
Red-alert security measures include the following:
If your access point allows this, lower your broadcast strength. The lower your broadcast strength is, the less likely a nefarious evildoer outside your network is to be able to intercept it.
Understand the range of your Wi-Fi broadcasts, and see if there are any obvious vulnerabilities (a parking lot? a neighbor who hates you?).
Regularly review the DHCP logs provided by your router to see if there are any unauthorized connections.
Turn off wireless access to the access point's administrative application (this is usually only available with enterprise-class Wi-Fi access points).
Use a dynamic, per-session WEP encryption scheme. This is usually only available with enterprise-class Wi-Fi access points, and may require additional hardware such as an authentication server.
Authenticate Wi-Fi connections with user names and passwords using a network directory server, or an authentication server.
Encourage access to your Wi-Fi network via a VPN (see Chapter 18, and the section later in this chapter, "Setting Up a VPN," for more details about VPNs).
Create a network topology that uses a DMZ with its own set of firewalls for the Wi-Fi access point (see Chapter 15 for more about DMZs and network topologies). This will isolate the access points from possible attacks. You can beef this up even further by making sure that the access point and the nodes on your wireless network can only communicate via a VPN. A good piece of equipment to use to implement this in the small office context is the Watchguard SoHo Firebox, which combines a firewall and a VPN, and costs about $300.








