Beginning the FireWall-1 Installation
Once you have properly installed, configured, and secured your operating system, you are ready to proceed with installation of the firewall software. The installation instructions included in the Getting Started guide as part of your Check Point documentation explain the specific steps necessary to load the software from the CD or from a tarball downloaded from Check Point's Software Subscription section. Check Point now distributes complete releases with each feature pack and does not require you to install a "base" release for a new installation.[3]
[3] A notable exception to this is NG FP2: While it is possible to install NG FP2 as a standalone release, it actually installs NG FP1 first, then upgrades it to NG FP2. On a Nokia platform, you will see NG FP1 and NG FP2 packages loaded on your platform. Removing the NG FP1 packages is a bad idea.
When downloading the software from Check Point's Software Subscription site, there are two ways to download it: as individual packages or as a "wrapper." Usually, installation via the wrapper is best because it will automatically load selected packages in the correct order. On the other hand, the wrapper contains every single package in the Check Point suite?some of which you may not use.
NOTE!
There appears to be a problem with the NG FP3 installation wrapper on IPSO: It will not correctly install the Desktop Policy Server for Secure Client. In this case, you will need to uninstall the Desktop Policy Server package and reinstall the Desktop Policy Server from the individual package. The package will then install correctly. |
For the purposes of demonstration, I will show the process for installing NG FP3 on a separate management console and firewall module. The management console will be loaded on a Windows 2000 platform. The firewall module will be loaded on a Nokia IP350. While it may seem strange that I don't show the process on other platforms as well, I can assure you the questions asked of you during installation will be almost identical.
Installing an NG FP3 Management Console on Windows 2000
In this example, NG FP3 is being installed via the installation wrapper. Installing the individual packages is basically the same except that you must choose to install each package manually. First, you would install the SVN Foundation package. Next, you would install the VPN-1/FireWall-1 package. Finally, you would install other packages as needed.
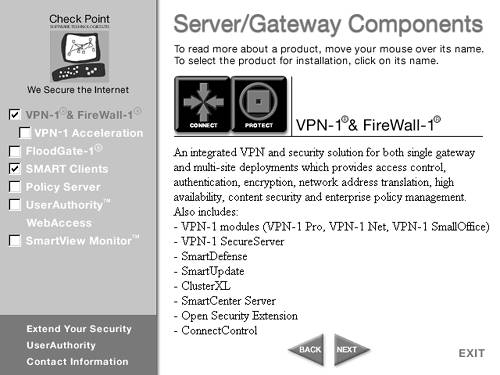
The installation wrapper allows you to choose which packages you wish to install. After clicking on the NG FP3 setup.exe for the wrapper installation, you are prompted to install Gateway Components or Desktop Components. Select Gateway Components. Then you can choose which components you want to install. A dialog similar to Figure 3.1 appears. For this example, you're installing a management station on this platform and not a firewall module, so the only checkboxes you need to select are VPN-1 & FireWall-1 and SMART Clients.
Figure 3.1. Choosing the components to install
After clicking Next, you see a screen similar to Figure 3.2, which simply confirms your choices. Click Next.
Figure 3.2. Verifying the components you wish to install
You then are presented with a screen similar to Figure 3.3. You can choose whether this is a firewall module, a management server, or a log server. A log server is a platform on which only logs are stored. A management server is also a log server, so that option is redundant when you've selected a management server. A machine can be both a firewall module and a management server. This is actually required for some licenses. In this case, select only the management server. Click Next.
Figure 3.3. Choosing the management console and/or the FireWall-1 module
Figure 3.4 shows the next screen, which allows you to choose whether this is a primary management station or a secondary management station. In most cases, you will select primary. If you are using Management High Availability and this is a secondary management station, you will select the secondary option instead. Click Next.
Figure 3.4. Specifying a primary management station
Figure 3.5 shows the next screen, which allows you to choose whether to install the Backward Compatibility package. This option is necessary only if your management station will be used to manage FireWall-1 4.1 firewalls. In this case, select the option "Install without backward compatibility." The management station thus will not manage FireWall-1 4.1 firewalls. Click Next.
Figure 3.5. Choosing to install FireWall-1 without backward compatibility
The next screen, shown in Figure 3.6, allows you to select an installation directory for FireWall-1. The default is usually what you want to specify, but if you decide not to install in the default location, make sure you choose an installation path that does not contain any spaces or you will likely have difficulties later. Click Next.
Figure 3.6. Choosing an installation directory for FireWall-1
After the VPN-1 & FireWall-1 software load, you are presented with a choice of installation directory for the SMART Clients, as shown in Figure 3.7. This may be installed anywhere you choose. Click Next.
Figure 3.7. Choosing an installation directory for SMART Clients
Figure 3.8 shows that you are then presented with several choices for which GUI applications to install. It is generally safe to install all the GUI applications, however, you may not wish to for one reason or another. Select the applications appropriate for your installation and click Next.
Figure 3.8. Choosing which SMART Clients to install
Next, you are presented with a screen to add licenses, as shown in Figure 3.9. If you do not have a license to add, a 15-day evaluation license will be generated later and you can click on Next. If you do have a license, click on the Add button and enter the details, similar to what is shown in Figure 3.10. Click OK, then Next.
Figure 3.9. Installing licenses
Figure 3.10. Adding a new license
Now add an administrative user so that the initial policy can be constructed; see Figure 3.11. (The role of this administrative user is described in Chapter 4.) Click OK, then Next.
Figure 3.11. Adding a new administrator
You want to add the IP addresses of any client machines that will have the SMART Clients loaded on them and will require access to the management station, as shown in Figure 3.12. The local management console is already included, so you need not specify it here. Click Next.
Figure 3.12. Adding remote management IP addresses
You are then prompted to type a bunch of random keystrokes, as shown in Figure 3.13. This seeds the random number generator for internal certificate authority functions, such as those needed by the Secure Internal Communication (SIC) process, which is described in more detail in Chapter 7. Click Next.
Figure 3.13. Random keystroke session
You need to click on the Initialize and Start Certificate Authority button, as shown in Figure 3.14. This is necessary for SIC to be used, which is needed to establish communication with other Check Point modules. The Internal Certificate Authority (ICA) is also used for issuing VPN-related certificates.
Figure 3.14. Establishing the Internal Certificate Authority
If you did not install a license, you will see a dialog similar to Figure 3.15. A 15-day evaluation license generated by the software is used in this case. Get a permanent license as soon as possible if you see this message.
Figure 3.15. Dialog showing the 15-day evaluation license message
In this example, the hostname picked up by the installation program was not a fully qualified domain name (FQDN). To ensure that the ICA will function correctly, you need to change the FQDN shown in the Certificate Authority window to match what is appropriate for your system. Click on the Change Management FQDN button. In the example shown in Figure 3.16, I have set the name to kermit.phoneboy.com. Click on Send to CA. Click on Next.
Figure 3.16. Changing the FQDN of the management station
Now you are presented with a fingerprint you can use to validate that you have connected to the right management station with the SMART Clients. An example is shown in Figure 3.17. Click Finish.
Figure 3.17. Fingerprint of the management station
When the installation is completed, you will see a dialog similar to Figure 3.18. If you are going to install a hotfix (e.g., NG FP3 Hotfix-2 or a Hotfix Accumulator), do not reboot, and install it now. After the installation, reboot your computer. Otherwise, select the Yes radio button and reboot now.
Figure 3.18. Installation completed
Installing an NG FP3 firewall module on an IP350
In this example, we will use the installation wrapper for IPSO to load NG FP3 as a firewall module on an IP350. On other UNIX platforms, the installation wrapper presents a text-based installation screen where you can choose which package(s) you want to install. In IPSO, all of the packages are automatically loaded, but only SVN Foundation and VPN-1/FireWall-1 are enabled by default. The other packages may be enabled as necessary in Voyager. For the purposes of this example, we do not need to configure anything in Voyager because the default packages suffice.
If the packages were loaded by the command line (e.g., newpkg), you will need to log out of your terminal session and log back in as admin or root. If the command echo $CPDIR shows something like /opt/CPshared-50-03, you are ready to proceed. If not, the package load did not proceed correctly. In IPSO, ensure that CPShared and FireWall-1 are actually marked as active.
Now type the command cpconfig. You are then presented with a license agreement. Once you have read and accepted the license agreement, you are presented with several choices for installation type, as shown below.
Select installation type: ------------------------- (1) Enforcement Module. (2) Enterprise Management. (3) Enterprise Management and Enforcement Module. (4) Enterprise Log Server. (5) Enforcement Module and Enterprise Log Server. Enter your selection (1-5/a-abort) [1]:
Since this will be a firewall module only, select Enforcement Module, option 1.
Next, you will be asked:
Would you like to install a Check Point clustering product (CPHA, CPLS or State Synchronization)? (y/n) [n] ?
If you plan to install this firewall module in a HighAvailability (HA) pair using VRRP, IP Clustering) or a Check Point HA product,[4] you should select "yes" here. In this example, I would choose "no" because the module I am installing this on will not be used for HA.
[4] Check Point HA products, except those built into VPN-1/FireWall-1 or IPSO itself, are not available on Nokia platforms. This is for the more general case on other UNIX-type platforms.
Next, you will be told several things.
IP forwarding disabled Hardening OS Security: IP forwarding will be disabled during boot. Generating default filter Default Filter installed Hardening OS Security: Default Filter will be applied during boot.
In order, these items mean the following.
The system has disabled IP forwarding. This means that the underlying operating system will not forward packets that aren't destined for itself.
To go one step further, the system has disabled IP forwarding at boot time. This means the system will not forward packets until FireWall-1 has loaded with a nondefault security policy.
The system has loaded a default filter, which blocks all traffic to the firewall unless it is a response to a valid connection originating from the firewall.
The system will load this new default filter at boot time.
The next step is to enter the licenses. The following example shows how to enter the license and the details manually. Central licensing is discussed in Chapter 7.
Configuring Licenses... ======================= Host Expiration Signature Features Note: The recommended way of managing licenses is using SmartUpdate. cpconfig can be used to manage local licenses only on this machine. Do you want to add licenses (y/n) [y] ? y Do you want to add licenses [M]anually or [F]etch from file: m IP Address: 1.2.3.4 Expiration Date: 01Feb2003 Signature Key: dfMBwazxr-tbbHRxN2v-DnxgHNJkA-LQAXycV3i SKU/Features: CPMP-EVAL-1-IKE3DES-NG CK-ABCD1234567890 License was added successfully
Now you have to generate some system entropy, that is, the random pool that will be used for various cryptographic functions, including authentication between the firewall and management server. Randomly press letter keys at random intervals until the system tells you to stop.
Configuring Random Pool...
==========================
You are now asked to perform a short random keystroke session.
The random data collected in this session will be used in
various cryptographic operations.
Please enter random text containing at least six different
characters. You will see the '*' symbol after keystrokes that
are too fast or too similar to preceding keystrokes. These
keystrokes will be ignored.
Please keep typing until you hear the beep and the bar is full.
[....................]
Thank you.
Finally, you must establish a one-time password for SIC, which will be used to authenticate the management station to the firewall module. Once this one-time password is used, all further authentication will be done with certificates.
Configuring Secure Internal Communication... ============================================ The Secure Internal Communication is used for authentication between Check Point components Trust State: Uninitialized Enter Activation Key: Again Activation Key: The Secure Internal Communication was successfully initialized
A new default filter will be compiled?one that permits management traffic to the firewall module. This policy will apply until the first real security policy is installed from the management station.
initial_module: Compiled OK. Hardening OS Security: Initial policy will be applied until the first policy is installed
Finally, you must reboot the system to properly install FireWall-1.
In order to complete the installation
you must reboot the machine.
Do you want to reboot? (y/n) [y] ? y






