What You Can Do with Remote Management
This section explains what you can do with the command line once remote management is configured correctly. Many of these commands can be executed when the management module and firewall module are on the same machine as well. See also the various command-line functions documented in Chapter 5.
Controlling Policy on a Firewall Module
A management module can load or unload a policy from a firewall module. The Security Policy Editor is normally used to do this, but this task can also be initiated from the command line on the management module. With a large and/or complex policy, you should load the policy from the command line because it takes far less time than using the GUI.
To load a policy from the management module to the firewall module, use the command fwm load as shown in the following example. (Note that snuffleupagus is the name of the management module and oscar is the firewall.)
C:\WINNT\FW1\NG\conf>fwm load pb-simple2.W oscar
pb-simple2.W: Security Policy Script generated into pb-simple2.pf
pb-simple2:
Compiled OK.
Installing Databases on: localhost
Database installed successfully on snuffleupagus...
Database installation complete
Database installation succeeded for:
snuffleupagus
Installing CPMAD Policy On: localhost
CPMAD policy installed successfully on snuffleupagus...
CPMAD policy installation complete
CPMAD policy installation succeeded for:
snuffleupagus
Installing VPN-1/FireWall-1 policy on: oscar ...
Connection templates will not be offloaded to the SecureXL
accelerator due to restrictions defined in the rulebase.
VPN-1/FireWall-1 policy installed successfully on oscar...
VPN-1/FireWall-1 policy installation complete
VPN-1/FireWall-1 policy installation succeeded for:
oscar
C:\WINNT\FW1\NG\conf>
To unload the policy on the remote firewall module from the management module, use the command fwm unload as shown in the following example.
C:\WINNT\FW1\NG\conf>fwm unload oscar
Uninstalling Policy From: oscar
VPN-1/FireWall-1 policy successfully uninstalled from oscar...
VPN-1/FireWall-1 policy uninstall complete.
C:\WINNT\FW1\NG\conf>
On the remote firewall module, you can fetch the last installed policy from the management module by using the fw fetch command as shown in the following example.
oscar[admin]# fw fetch snuffleupagus
Fetching Security Policy From: snuffleupagus
Local Policy is Up-To-Date.
Reinstalling Local Policy.
Installing Security Policy pb-simple2 on all.all@oscar
Fetching Security Policy Succeeded
oscar[admin]#
NOTE!
If you're familiar with FireWall-1 4.1 and earlier versions, you may have noticed that fwm is now used to manipulate the policy from the management station instead of fw. You can still use fw, though you will get an error message declaring the command obsolete. For fetching a policy from the management module, however, fwm cannot be used and will generate a usage message. |
Viewing State Tables of Firewall Modules
The fw tab commands can be run from the management module to check the state tables on a firewall module. A few tables of interest include the connections table and the address translation tables. The following command shows you the contents of the connections table on oscar:
# fw tab
oscar:
-------- connections --------
dynamic, id 8158, attributes: keep, sync, expires 25,
refresh, limit 25000, hash size 32768, kbuf 16 17 18
19 20 21 22 23 24 25 26 27 28 29 30, free function a47ed69c 0
<00000000, 0a0000ff, 00000208, 0a000001, 00000208, 00000011,
28203a0a> -> <00000001, 0a000001, 00000208, 0a0000ff,
00000208>(00000011)
<00000001, 0ad02001, 00000043, ffffffff, 00000044, 00000011,
28203a0a> -> <00000000, 0ad02001, 00000043, ffffffff, 00000044>
(00000011)
<00000001, 0a0000ff, 0000007b, 0a0000fe, 0000007b, 00000011,
6c61763a> -> <00000000, 0a0000fe, 0000007b, 0a0000ff, 0000007b>
(00000011)
<00000001, 0a000002, 000011c1, 3f6f1665, 00000016, 00000006,
6f745f6b> -> <00000000, 0a000002, 000011c1, 3f6f1665, 00000016>
(00000006)
<00000001, d82f7135, 00000016, 0a000002, 000011be, 00000006,
5f41535f> -> <00000000, 0a000002, 000011be, d82f7135, 00000016>
(00000006)
<00000000, 0a000009, 00000dd7, 04164206, 00000050, 00000006,
32303128, 0a293030, 203a0a29, 54324c28, 75745f50, 6c656e6e,
6d6c5f73, 79743a0a, 28206570, 29746e69, 0001f001, 00806000,
00000006, 00000e10, 00000000, 3e8774d4, 00000000; 0001f001,
00806000, 00000006, 00000e10, 00000000, 3e8774d4; 9/20>
<00000001, 0a000001, 00000208, 0a0000ff, 00000208, 00000011,
61763a0a, 3228206c, 0a293030, 203a0a29, 73776628, 74616e79,
656d5f6b, 646f6874, 79743a0a, 28206570, 00020001, 00806000,
00000006, 00000028, 00000000, 3e8774a4, 00000000; 00020001,
00806000, 00000006, 00000028, 00000000, 3e8774a4; 17/40>
<00000001, 04164206, 00000050, 0a000009, 00000dd7, 00000006,
616e5f72> -> <00000000, 0a000009, 00000dd7, 04164206, 00000050>
(00000006)
<00000000, 3f6f1665, 00000016, 0a000002, 000011c1, 00000006,
725f7469> -> <00000000, 0a000002, 000011c1, 3f6f1665, 00000016>
(00000006)
<00000001, ffffffff, 00000044, 0ad02001, 00000043, 00000011,
61662820> -> <00000000, 0ad02001, 00000043, ffffffff, 00000044>
(00000011)
<00000000, d82f7135, 00000016, 44740502, 00006b64, 00000006,
62282065> -> <00000000, 0a000002, 000011be, d82f7135, 00000016>
(00000006)
<00000001, 44740502, 00000100, 0a000009, 00000de1, 00000006,
61645f67> -> <00000000, 0a000009, 00000de1, 44740502, 00000100>
(00000006)
<00000000, d82f7135, 00000016, 0a000002, 000011be, 00000006,
6628203a> -> <00000000, 0a000002, 000011be, d82f7135, 00000016>
(00000006)
<00000000, 3f6f1665, 00000016, 44740502, 00006b66, 00000006,
3a0a290a> -> <00000000, 0a000002, 000011c1, 3f6f1665, 00000016>
(00000006)
<00000001, 3f6f1665, 00000016, 0a000002, 000011c1, 00000006,
61636464> -> <00000000, 0a000002, 000011c1, 3f6f1665, 00000016>
(00000006)
<00000000, 0a0000fe, 0000007b, 0a000001, 0000007b, 00000011,
206c6176> -> <00000001, 0a000001, 0000007b, 0a0000fe, 0000007b>
(00000011)
...(20 More)
NOTE!
The first six items in each connections table entry are direction (0 is inbound, 1 is outbound), source IP, source port, destination IP, destination port, and IP protocol number. They are all in hexadecimal. You can find a complete description of all other entries in the connections table in Check Point's Advanced Technical Reference Guide, available from http://www.checkpoint.com/support/technical/documents/atrg-ngfp3/pdf/cpts-doc-atrg-01-s-ngfp3.pdf. You need a valid software subscription agreement to view these documents. You may also purchase this document from Check Point Education Services via the following order form: https://www.checkpoint.com/services/education/courseware/OrderHomePage.jsp. |
You can also get just a count of the number of entries in a few tables if that is all you are interested in:
C:\WINNT\FW1\NG\conf> fw tab -t connections -t fwx_alloc ?s oscar
HOST NAME ID #VALS #PEAK #SLINKS
oscar connections 8158 14 33 33
oscar fwx_alloc 8187 10 107 0
ID is an internal identifier for the table, #VALS means the number of entries, #PEAK is the "high-water mark" for the number of entries in this table, and #SLINKS shows the number of symbolic links present in the connections table (each connection actually generates more than one entry).
WARNING!
There appears to be a bug in FireWall-1 NG FP3 that causes these kinds of queries from the management station to return bogus results. Queries from the local firewall module return the correct results. |
Updating Licenses
You can view, retrieve, and edit licenses for remote firewall modules from a management module. In addition to command-line functionality, it is also possible to manage licenses from SmartUpdate. Instead of presenting a table that explains the commands, I will take you through the process of replacing a license on a module for the first time, which will show you all the commands.
First we should get the licenses from all the nodes by using the command cprlic get ?all. If we want to get licenses from a specific module, we can use the command cprlic get modulename. If any of the modules are running FireWall-1 4.1, we need to use the ?v41 flag. In any case, this brings all of the licenses installed on these modules into the repository.
Now we should see which licenses are present. The command cprlic print ?all ?x ?t ?a prints all licenses installed on all platforms (-all), print signatures (-x), print license type (-t), and where the license is attached (-a). Optionally, -all can be replaced with the relevant module name. The other command-line options are optional but recommended to obtain the most information.
C:\ > cprlic print -all -x -t -a
The following licenses appear in the database:
===============================================
Host Expiration Features
eval 05May2003 dZCTqLvXYp3ytGaJDe9tRxLDCAQjdMPx4Pab
CPMP-MEDIA-1-NG CK-CP central snuffleupagus oscar
eval 01Mar2003 d7uXL9CypXoNpAqubgjvN7N5EoE6nE6LbBff
CPMP-EVAL-1-3DES-NG CK-CP central oscar
When the preceding output was generated, the date was March 30, 2003. This means the eval license dated 01Mar2003 is expired and can be safely removed from the system. To do this, we must first detach the license from oscar (the module on which it is installed), then remove it.
To remove the license, we use the command cprlic del oscar d7uXL9CypXoNpAqubgjvN7N5EoE6nE6LbBff. We must specify the module name and the "signature" of the license in question. If the module has a dynamic IP address, we use the ?p option and specify the current IP address of the module. When the command completes, we get a list of licenses attached to the specified module.
A cprlic print ?all ?x ?t ?a command now shows different output:
C:\> cprlic print -all -x -t -a
The following licenses appear in the database:
===============================================
Host Expiration Features
eval 05May2003 dZCTqLvXYp3ytGaJDe9tRxLDCAQjdMPx4Pab
CPMP-MEDIA-1-NG CK-CP central snuffleupagus oscar
eval 01Mar2003 d7uXL9CypXoNpAqubgjvN7N5EoE6nE6LbBff
CPMP-EVAL-1-3DES-NG CK-CP central
Notice that the 01Mar2003 license is now no longer attached to oscar. Since it is no longer attached to any module, we can remove it using the cprlic rm command. We specify this license by signature again as shown below:
C:\> cprlic rm d7uXL9CypXoNpAqubgjvN7N5EoE6nE6LbBff Are you sure you want to delete this license? [y/n] : y Operation complete. License deleted from database.
Now we will add a new license to the repository for the firewall module. We do this with cprlic add.
C:\> cprlic add 10.0.0.9 30May2003 d3uDEt3jb-pPgE8ZEyd- hBNMH5AvT-SkCJJEMgn CPMP-EVAL-1-3DES-NG CK-1337DEADD00D Operation Done.
Now we can install the license on the module with cprlic put as shown below:
C:\> cprlic put oscar 10.0.0.9 30Apr2003 d3uDEt3jbpPgE8ZEydhBNMH5AvTSkCJJEMgn CPMP-EVAL-1-3DES-NG CK-D1790E4B08B4 Operation Done. The following licenses are attached to oscar ============================================== Host Expiration Features eval 05May2003 CPMP-MEDIA-1-NG CK-CP 10.0.0.9 30May2003 CPMP-EVAL-1-3DES-NG CK-1337DEADD00D
To make life even easier, all of these functions can be done via the SmartUpdate GUI as well. Figure 7.3 shows you the SmartUpdate Licenses tab in NG FP3.
Figure 7.3. SmartUpdate Licenses tab
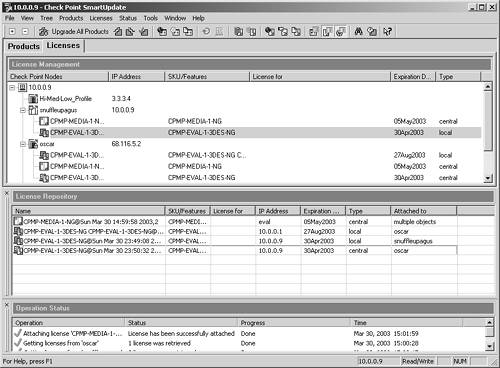
To get the view shown in Figure 7.3, you must select View Repository from the Licenses menu. With the License Repository window showing, you can simply right-click anywhere in it and add new licenses, detach a license (provided you are clicking on a license), export licenses, or view the license. You can also drag and drop licenses from the License Repository window to the modules on which you wish to install the licenses. Right-clicking on a license in the License Management window allows you to detach the license or export it to a file.






