Group Policy Management User Interface
In Windows 2000 only one utility is available for managing Group Policy?the Group Policy MMC snap-in. Windows Server 2003 not only expands on this utility, but also introduces some additional utilities for Group Policy management.
Group Policy Object Editor
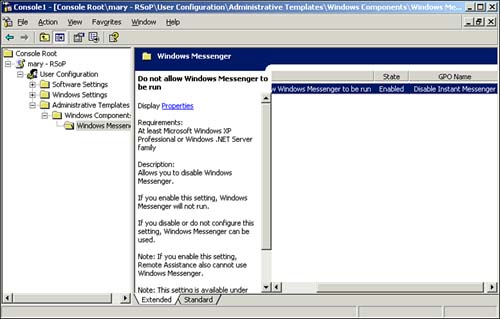
The old Group Policy snap-in has been renamed Group Policy Object Editor. The MMC interface has been improved to use a Web style interface. Two choices of view exist for the right policy list pane: Standard, which is the old Windows 2000 style, and Extended, which is the new style. When using the Extended style, an explanation of what the policy does is displayed when a policy listed in the right pane is clicked. This helps you more easily determine what each of the policies does. As shown in Figure 6.4, in addition to a description of the policy, a Requirements section lists the systems that support the policy (Windows 2000, XP, .NET, and so on). This enables you to easily tell which policies apply to particular systems.
Figure 6.4. The Group Policy Object Editor (Formerly the Group Policy snap-in) displaying the OS requirements and descriptive information for the DNS dynamic update policy.
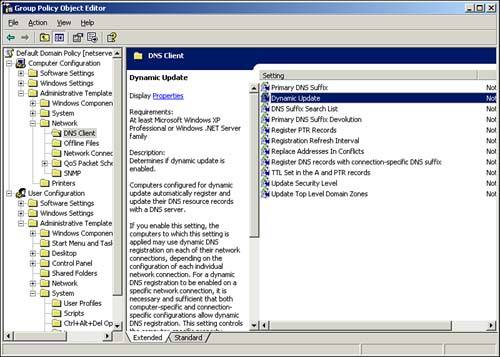
NoteThe new Extended tab is not available for the Security Options section, and no Description or Requirements headings exist. The policies in this section are viewed the same as in Windows 2000. |
Because Group Policy is now supported by multiple operating systems (Windows 2000, Windows XP, and Windows Server 2003) and some policies are applicable only for some of these operating systems, a new Filtering option is available on the View menu for Administrative Templates. This option enables you to limit the policies that are displayed in the Group Policy Editor MMC. They can be filtered to do the following:
Filter by Requirements Information? Shows only those policies supported by a particular operating system or specific applications. For example, by clicking the check boxes for At Least Windows 2000 Service Pack 1 and At Least Internet Explorer 6 Service Pack 1, you display only those policies that can be used on systems with Windows 2000 SP1 and IE6.
Only Show Configured Policy Settings? Displays only policies that are currently configured in the particular GPO.
Only Show Policy Settings that Can Be Fully Managed? Hides Windows NT 4.0 system polices that might have been loaded as administrative templates.
Resultant Set of Policy
By now, you can probably get a sense for the bewildering array of Group Policy settings. Because of all the Group Policy application rules?inheritance, block inheritance, no override, filtering (by group or WMI filter), and so on?troubleshooting Group Policy applications can be a nightmare. A new utility can help: the Resultant Set of Policy (RSoP) MMC snap-in. RSoP enables you to see the effects of group policies. As shown in Figure 6.5, the RSoP console displays each Group Policy setting that applies as well as the source GPO from which the policy was obtained.
Figure 6.5. The Resultant Set of Policy console displays effective user rights policy settings and the GPOs from which they were applied.
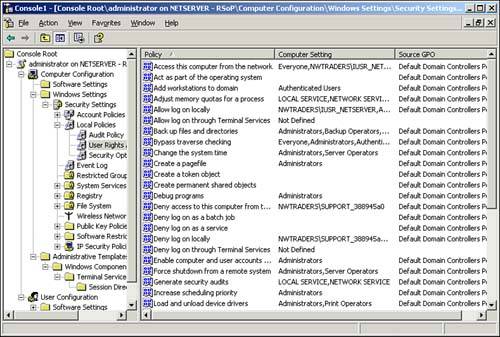
NoteNo Resultant Set of Policy console is available on the default Administrative Tools menu. You must therefore create your own RSoP MMC console. Additionally, the first time the snap-in is used, no data is displayed because no queries have been run yet. You have to launch the Resultant Set of Policy Wizard by right-clicking Resultant Set of Policy and selecting Generate RSoP Data. This launches the wizard, which walks you through the prompts for generating the scenario for which you want to examine Group Policy data. |
For a tutorial on how to create Microsoft Management Consoles (MMC), visit www.samspublishing.com and enter this book's ISBN number (no hyphens or parenthesis) in the Search field; then click the book cover image to access the book details page. Click the Web Resources link in the More Information section, and locate article ID# A011301. |
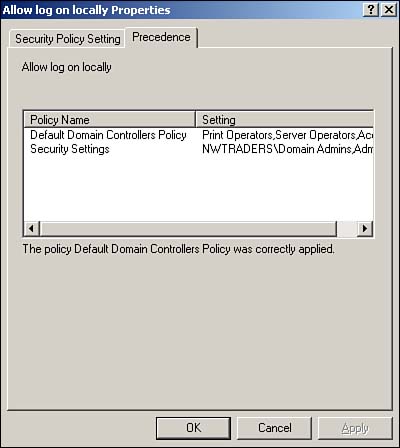
Additionally, youcan right-click any of these settings and select Properties. This brings up the configurable options for the policy setting, just like in Group Policy Editor. However, a Precedence tab is also available, as shown in Figure 6.6. This tab shows all the GPOs that apply that setting. This helps determine whether any kind of GPO conflict exists and whether policies are being applied as expected. In this case, two policies (Default Domain Controller Policy and Security Settings) configure the Allow Log on Locally setting. From Figure 6.6 you can see that the Default Domain Controller Policy wins the conflict.
Figure 6.6. The Precedence tab for policy settings allows you to determine at a glance whether a policy conflict exists.
The RSoP console has two modes for displaying policy data, Logging and Planning. Logging mode enables you to see the current policies applied to a particular user and machine. Planning mode, on the other hand, enables you to run what-if scenarios to see the effective policies. The variables that you can manipulate in the what-if scenarios are as follows:
User configuration policy settings for a particular user or container
Computer configuration policy settings for a particular computer or container
Group Policy environment settings?slow WAN link, loopback processing, Active Directory site
Group membership
WMI filters
By manipulating these variables, administrators can determine the effects of Group Policy changes without actually performing them. For example, how are policies affected if a user is moved from one OU to another? What if she accesses the network from a different site? What if you add her to a particular group or apply a WMI filter? And so on.
Planning mode needs to query Active Directory to determine the policies applied in these various circumstances. Consequently, Planning mode is available only if the machine running the RSoP console is a member of an Active Directory domain.
In the following example, you will use RSoP to examine the user configuration policy applied to a particular user. Then you will run RSoP again to see what would happen if you moved the user to a different OU.
NoteFor this scenario, I have created a user called Mary in the Users container. Mary is only a member of the default Domain Users group, and the only policies are the default policies (Default Domain Policy applied at the domain level and Default Domain Controllers Policy applied at the Domain Controllers OU) with the default settings. I have also created an OU called Employees that has a Group Policy (Disable Instant Messenger) that is configured with a User Configuration Administrative Template setting to not allow Windows Messenger to be run. To get the same results when following along with this example, you should also create these objects (in a test environment, of course). |
First, let's see what settings are currently being applied to Mary. Do the following:
Create an MMC console with the Resultant Set of Policy snap-in.
Right-click Resultant Set of Policy and select Generate RSoP Data.
On the Welcome to the Resultant Set of Policy Wizard screen, click Next.
On the Mode Selection screen, make sure Planning Mode is selected and click Next.
Select User and then click Browse.
Make sure Current User is selected and click Next.
On the Select User screen, type in Mary in the Enter the Object Name to Select(Examples): field and click Check Names. The name should resolve to something like Mary(mary@nwtraders.msft). Click OK.
Because you are not interested in changing anything and just want to see the user's current settings, select Skip to the Final Page of This Wizard Without Collecting Additional Data and click Next.
Click Next on the Summary of Selections screen.
Click Finish.
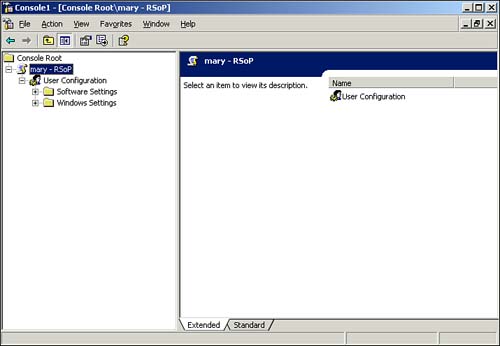
As shown in Figure 6.7, the RSoP console displays all the User Configuration policy settings that are being applied to Mary. There are no Administrative Template settings at all, so the user currently has no policy restricting Windows Messenger.
Figure 6.7. The Resultant Set of Policy in logging mode displaying all the policies applying to the user.
Next, let's look at what happens to the policy settings if you move Mary to the Employees OU. Follow these steps:
Because you have already run a query once in the RSoP console, right-click the username (mary-RSoP) and select Change Query.
On the Resultant Set of Policy Wizard screen, click Next.
Because you're not doing anything with her site or WAN links, on the Advanced Simulation Options screen, click Next.
On the Alternate Active Directory Paths screen, select Browse. This is where you get to move Mary to a new OU.
On the Choose User Container screen, find and select the Employees OU; then click OK. On the Alternate Active Directory Paths screen, the distinguished name of the Employees OU should now be listed under User location. Click Next.
Because you're only moving Mary to a new OU and not making any other changes, click Next on the User Security Groups screen.
Click Next on the WMI Filters for Users screen.
Click Next on the Summary of Selections screen.
Click Finish.
Now, as shown in Figure 6.8, RSoP displays the effective Group Policy settings when the user is moved to the OU. Note that there is now an Administrative Templates section. In addition, the Do Not Allow Windows Messenger to Run policy is enabled, and it was obtained from the Disable Instant Messenger GPO. Also, remember that you did not actually move Mary's account?this just lets you see what would happen if you did.
Figure 6.8. The Resultant Set of Policy in Planning mode displaying the policies that would be applied to Mary if you moved her account.
Group Policy Management Console
Yet another new utility is available for Group Policy management?the Group Policy Management Console (GPMC). Unfortunately, it is not included with Windows Server 2003. However, it is supposed to be available as a free download when Windows Server 2003 is released. Once installed, GPMC replaces the existing Group Policy Object Editor on the Group Policy tab objects (sites, domains and OUs) in Active Directory Users and Computer.
GPMC provides a single console for managing GPOs across multiple forests. As shown in Figure 6.9, the tree pane view shows all the Group Policy objects throughout the entire forest. For each forest, there is a display of the domain, OU, and site hierarchies, which allow you to see all the GPOs linked at each level. Additionally for each domain, a Group Policy Objects and WMI Filters section shows all existing GPOs and WMI filters, respectively, whether they are linked or not.
Figure 6.9. The Group Policy Management Console displaying GPOs for a single domain forest.
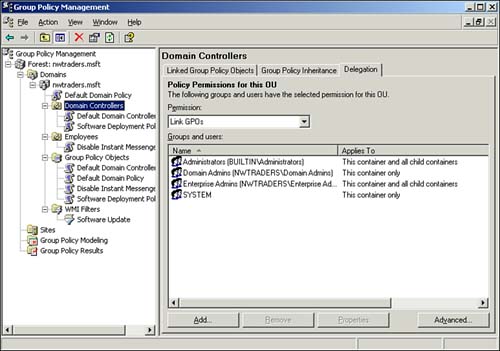
In the tree-pane view of the hierarchy, you can see which policies are linked to each location simply by clicking the location, such as the Domain Controllers OU, and viewing the Linked Group Policy Objects tab. The Group Policy Precedence tab displays all the group policies that will be processed at the particular location, including those inherited from parent containers, and the order in which they will be processed. This enables you to see at a glance whether any conflicts might arise. The Delegation tab displays who has permissions (Link GPOs, Perform Group Policy Modeling Analysis, and Remotely Access Group Policy Results Data) to manage the GPOs at that particular level (site, domain, or OU).
By selecting a GPO, you can see where it is linked, whether it is enabled at the linked location, any filters that might be applied (by group or WMI filter), as well as any other permissions for the GPO. You can also right-click the policy and edit it, just like in Group Policy Object Editor. However, be careful because editing a GPO affects all locations where the policy is applied, just like when you edit with Group Policy Editor (it actually launches the Group Policy Object Editor to perform the edits).
Clicking a GPO in the Group Policy Objects container displays the same information as mentioned previously, but this section enables you to back up and restore your GPOs as well as import settings from previous backups into existing GPOs. Similarly, the WMI Filters container lists all the WMI filters configured?whether linked or not?and allows you to import and export them.
GPMC also integrates with RSoP via the Group Policy Modeling and Group Policy Results sections to provide reporting of RSoP data and GPO settings. The Group Policy Modeling and Group Policy Results sections correspond to RSoP Planning and Logging modes, respectively (they actually launch the RSoP wizards).
To top it all off, the GPMC is fully scriptable, so anything you can do in GPMC you can automate with a script. It also includes several sample scripts (C:\Program Files\GPMC\Scripts) for automating common GPO administrative tasks, such as creating and deleting GPOs.
The Group Policy Management Console is a complete rework of the Group Policy user interface and extremely simplifies Group Policy management. I strongly recommend every Group Policy administrator download and install the GPMC when it is available. If nothing else, it provides a unified view and centralized console for running all your Group Policy management utilities.







