Introduction to Relational Database Design
Many people believe Access is such a simple product to use that database design is something they don't need to worry about. I couldn't disagree more! Just as a poorly planned vacation will generally not be very much fun, a database with poorly designed tables and relationships will fail to meet the needs of its users.
The History of Relational Database Design
Dr. E. F. Codd first introduced formal relational database design in 1969 while he was at IBM. Relational theory, which is based on set theory and predicate logic, applies to both databases and database applications. Codd developed 12 rules that determine how well an application and its data adhere to the relational model. Since Codd first conceived these 12 rules, the number of rules has expanded into the hundreds. |
You should be happy to learn that, although Microsoft Access is not a perfect application development environment, it measures up quite well as a relational database system.
Goals of Relational Database Design
The number-one goal of relational database design is to, as closely as possible, develop a database that models some real-world system. This involves breaking the real-world system into tables and fields and determining how the tables relate to each other. Although on the surface this might appear to be a trivial task, it can be an extremely cumbersome process to translate a real-world system into tables and fields.
A properly designed database has many benefits. The processes of adding, editing, deleting, and retrieving table data are greatly facilitated in a properly designed database. In addition, reports are easy to build. Most importantly, the database is easy to modify and maintain.
Rules of Relational Database Design
To adhere to the relational model, you must follow certain rules. These rules determine what you store in a table and how you relate the tables. These are the rules:
The rules of tables
The rules of uniqueness and keys
The rules of foreign keys and domains
The Rules of Tables
Each table in a system must store data about a single entity. An entity usually represents a real-life object or event. Examples of objects are customers, employees, and inventory items. Examples of events include orders, appointments, and doctor visits. |
The Rules of Uniqueness and Keys
Tables are composed of rows and columns. To adhere to the relational model, each table must contain a unique identifier. Without a unique identifier, it is programmatically impossible to uniquely address a row. You guarantee uniqueness in a table by designating a primary key, which is a single column or a set of columns that uniquely identifies a row in a table. |
Each column or set of columns in a table that contains unique values is considered a candidate key. One candidate key becomes the primary key. The remaining candidate keys become alternate keys. A primary key made up of one column is considered a simple key. A primary key composed of multiple columns is considered a composite key. |
It is generally a good idea to choose a primary key that is
Minimal (has as few columns as possible)
Stable (rarely changes)
Simple (is familiar to the user)
Following these rules greatly improves the performance and maintainability of a database application, particularly if it deals with large volumes of data.
Consider the example of an employee table. An employee table is generally composed of employee-related fields such as Social Security number, first name, last name, hire date, salary, and so on. The combination of the first name and the last name fields could be considered a primary key. This might work until the company hires two employees who have the same name. Although the first and last names could be combined with additional fields (for example, hire date) to constitute uniqueness, that would violate the rule of keeping the primary key minimal. Furthermore, an employee might get married, and her last name might change. This violates the rule of keeping a primary key stable. Therefore, using a name as the primary key violates the principle of stability. The Social Security number might be a valid choice for primary key, but a foreign employee might not have a Social Security number. This is a case in which a derived, rather than a natural, primary key is appropriate. A derived key is an artificial key that you create. A natural key is one that is already part of the database. |
In examples such as this, I suggest adding EmployeeID as an AutoNumber field. Although the field would violate the rule of simplicity (because an employee number is meaningless to the user), it is both small and stable. Because it is numeric, it is also efficient to process. In fact, I use AutoNumber fields as primary keys for most of the tables that I build.
The Rules of Foreign Keys and Domains
A foreign key in one table is the field that relates to the primary key in a second table. For example, the CustomerID field may be the primary key in a Customers table and the foreign key in an Orders table.
A domain is a pool of values from which columns are drawn. A simple example of a domain is the specific data range of employee hire dates. In the case of the Orders table, the domain of the CustomerID column is the range of values for the CustomerID in the Customers table. |
Normalization and Normal Forms
Some of the most difficult decisions that you face as a developer are what tables to create and what fields to place in each table, as well as how to relate the tables that you create. As you learned in Hour 7, Normalization is the process of applying a series of rules to ensure that a database achieves optimal structure. Normal forms are a progression of these rules. Each successive normal form achieves a better database design than the previous form. Although there are several levels of normal forms, it is generally sufficient to apply only the first three levels of normal forms. The following sections describe the first three levels of normal forms. |
First Normal Form
To achieve first normal form, all columns in a table must be atomic. This means, for example, that you cannot store first name and last name in the same field. The reason for this rule is that data becomes very difficult to manipulate and retrieve if you store multiple values in a single field. Let's use the full name as an example. It would be impossible to sort by first name or last name independently if you stored both values in the same field. Furthermore, you or the user would have to perform extra work to extract just the first name or just the last name from the field. |
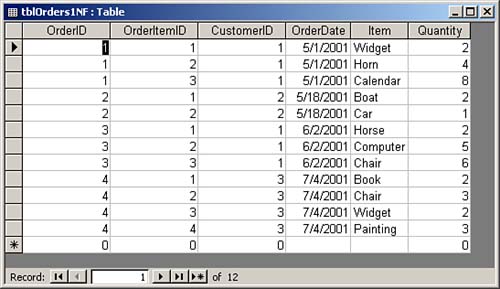
Another requirement for first normal form is that the table must not contain repeating values. An example of repeating values is a scenario in which Item1, Quantity1, Item2, Quantity2, Item3, and Quantity3 fields are all found within the Orders table (see Figure 9.1). This design introduces several problems. What if the user wants to add a fourth item to the order? Furthermore, finding the total ordered for a product requires searching several columns. In fact, all numeric and statistical calculations on the table are extremely cumbersome. Repeating groups make it difficult to summarize and manipulate table data. The alternative, shown in Figure 9.2, achieves first normal form. Notice that each item ordered is located in a separate row. All fields are atomic, and the table contains no repeating groups.
Figure 9.1. A table that contains repeating groups.
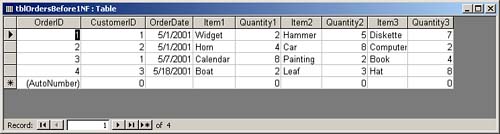
Figure 9.2. A table that achieves first normal form.
Second Normal Form
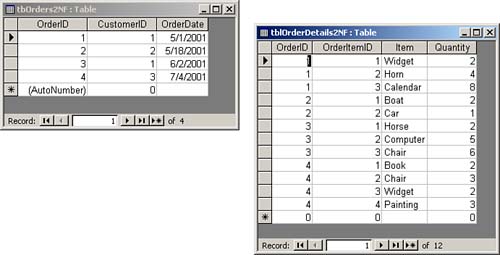
For a table to achieve second normal form, all non-key columns must be fully dependent on the primary key. In other words, each table must store data about only one subject. For example, the table shown in Figure 9.2 includes information about the order (OrderID, CustomerID, and OrderDate) and information about the items the customer is ordering (Item and Quantity). To achieve second normal form, you must break this data into two tables?an order table and an order detail table. The process of breaking the data into two tables is called decomposition. Decomposition is considered to be non-loss decomposition because no data is lost during the decomposition process. After you separate the data into two tables, you can easily bring the data back together by joining the two tables via a query. Figure 9.3 shows the data separated into two tables. These two tables achieve second normal form because the fields in each table pertain to the primary key of the table. |
Figure 9.3. Tables that achieve second normal form.
Third Normal Form
To attain third normal form, a table must meet all the requirements for first and second normal forms, and all non-key columns must be mutually independent. This means that you must eliminate any calculations, and you must break out the data into lookup tables. Lookup tables include tables such as inventory tables, course tables, state tables, and any other table where you look up a set of values from which you select the entry that you store in the foreign key field. For example, from the Customer table, you look up within the set of states in the state table to select the state associated with the customer.
An example of a calculation stored in a table is the product of price multiplied by quantity. Instead of storing the result of this calculation in the table, you would generate the calculation in a query or in the control source of a control on a form or a report.
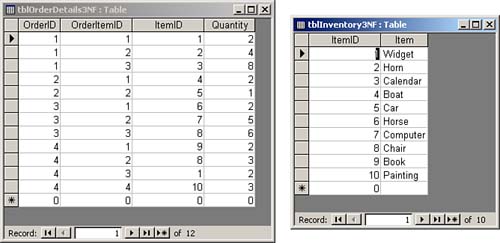
The example in Figure 9.3 does not achieve third normal form because the description of the inventory items is stored in the Order Details table. If the description changes, all rows with that inventory item need to be modified. The Order Details table, shown in Figure 9.4, shows the item descriptions broken into an Inventory table. This design achieves third normal form. We have moved the description of the inventory items to the Inventory table, and ItemID is stored in the Order Details table. All fields are mutually independent. You can modify the description of an inventory item in one place.
Figure 9.4. A table (on the right) that achieves third normal form.
Denormalization: Purposely Violating the Rules
Although a developer's goal is normalization, there are many times when it makes sense to deviate from normal forms. This process is called denormalization. The primary reason for applying denormalization is to enhance performance. |
An example of when denormalization might be the preferred tact could involve an open invoices table and a summarized accounting table. It might be impractical to calculate summarized accounting information for a customer when you need it. Instead, you can maintain the summary calculations in a summarized accounting table so that you can easily retrieve them as needed. Although the upside of this scenario is improved performance, the downside is that you must update the summary table whenever you make changes to the open invoices. This imposes a definite trade-off between performance and maintainability. You must decide whether the trade-off is worth it.
If you decide to denormalize, you should document your decision. You should make sure that you make the necessary application adjustments to ensure that you properly maintain the denormalized fields. Finally, you need to test to ensure that the denormalization process actually improves performance.
Integrity Rules
Although integrity rules are not part of normal forms, they are definitely part of the database design process. Integrity rules are broken into two categories: overall integrity rules and database-specific integrity rules.
Overall Integrity Rules
The two types of overall integrity rules are referential integrity rules and entity integrity rules. Referential integrity rules dictate that a database does not contain any orphan foreign key values. This means that |
Child rows cannot be added for parent rows that do not exist. In other words, an order cannot be added for a nonexistent customer.
A primary key value cannot be modified if the value is used as a foreign key in a child table. This means that a CustomerID in the Customers table cannot be changed if the Orders table contains rows with that CustomerID.
A parent row cannot be deleted if child rows have that foreign key value. For example, a customer cannot be deleted if the customer has orders in the Orders table.
Entity integrity dictates that the primary key value cannot be Null. This rule applies not only to single-column primary keys, but also to multicolumn primary keys. In fact, in a multicolumn primary key, no field in the primary key can be Null. This makes sense because if any part of the primary key can be Null, the primary key can no longer act as a unique identifier for the row. Fortunately, the Jet Engine does not allow a field in a primary key to be Null.
Database-Specific Integrity Rules
Database-specific integrity rules are not applicable to all databases, but are, instead, dictated by business rules that apply to a specific application. Database-specific rules are as important as overall integrity rules. They ensure that the user enters only valid data into a database. An example of a database-specific integrity rule is requiring the delivery date for an order to fall after the order date.
The Types of Relationships
Three types of relationships can exist between tables in a database: one-to-many, one-to-one, and many-to-many. Setting up the proper type of relationship between two tables in a database is imperative. The right type of relationship between two tables ensures
Data integrity
Optimal performance
Ease of use in designing system objects
The reasons behind these benefits are covered throughout this hour. Before you can understand the benefits of relationships, though, you must understand the types of relationships available.
One-to-Many Relationships
A one-to-many relationship is by far the most common type of relationship. In a one-to-many relationship, a record in one table can have many related records in another table. A common example is a relationship set up between a Customers table and an Orders table. For each customer in the Customers table, you want to have more than one order in the Orders table. On the other hand, each order in the Orders table can belong to only one customer. The Customers table is on the "one" side of the relationship, and the Orders table is on the "many" side. In order for you to implement this relationship, the field joining the two tables on the "one" side of the relationship must be unique. |
In the Customers and Orders tables example, the CustomerID field that joins the two tables must be unique within the Customers table. If more than one customer in the Customers table has the same customer ID, it is not clear which customer belongs to an order in the Orders table. For this reason, the field that joins the two tables on the "one" side of the one-to-many relationship must be a primary key or have a unique index. In almost all cases, the field relating the two tables is the primary key of the table on the "one" side of the relationship. The field relating the two tables on the "many" side of the relationship is the foreign key.
One-to-One Relationships
In a one-to-one relationship, each record in the table on the "one" side of the relationship can have only one matching record in the table on the "many" side of the relationship. This relationship is not common and is used only in special circumstances. Usually, if you have set up a one-to-one relationship, you should have combined the fields from both tables into one table. The following are the most common reasons to create a one-to-one relationship: |
The number of fields required for a table exceeds the number of fields allowed in an Access table.
Certain fields that are included in a table need to be much more secure than other fields in the same table.
Several fields in a table are required for only a subset of records in the table.
The maximum number of fields allowed in an Access table is 255. There are very few reasons a table should ever have more than 255 fields. In fact, before you even get close to 255 fields, you should take a close look at the design of the system. On the rare occasion when having more than 255 fields is appropriate, you can simulate a single table by moving some of the fields to a second table and creating a one-to-one relationship between the two tables.
The second reason to separate into two tables data that logically would belong in the same table involves security. An example is a table that contains employee information. Certain information, such as employee name, address, city, state, zip code, home phone, and office extension, might need to be accessed by many users of the system. Other fields, including the hire date, salary, birth date, and salary level, might be highly confidential. Field-level security is not available in Access. You can simulate field-level security by using a special attribute of queries called Run with Owner's Permissions. The alternative to this method is to place the fields that all users can access in one table and the highly confidential fields in another. You give only a special Admin user (that is, a user with special security privileges?not one actually named Admin) access to the table that contains the confidential fields. |
The last situation in which you would want to define one-to-one relationships is when you will use certain fields in a table for only a relatively small subset of records. An example is an Employees table and a Vesting table. Certain fields are required only for employees who are vested. If only a small percentage of a company's employees are vested, it is not efficient, in terms of performance or disk space, to place all the fields containing information about vesting in the Employees table. This is especially true if the vesting information requires a large number of fields. By breaking the information into two tables and creating a one-to-one relationship between the tables, you can reduce disk-space requirements and improve performance. This improvement is particularly pronounced if the Employees table is large.
Many-to-Many Relationships
In a many-to-many relationship, records in two tables have matching records. You cannot directly define a many-to-many relationship in Access; you must develop this type of relationship by adding a table called a junction table. You relate the junction table to each of the two tables in one-to-many relationships. For example, with an Orders table and a Products table, each order will probably contain multiple products, and each product is likely to be found on many different orders. The solution is to create a third table, called OrderDetails. You relate the OrderDetails table to the Orders table in a one-to-many relationship based on the OrderID field. You relate it to the Products table in a one-to-many relationship based on the ProductID field. |







